Table of Contents
VPN
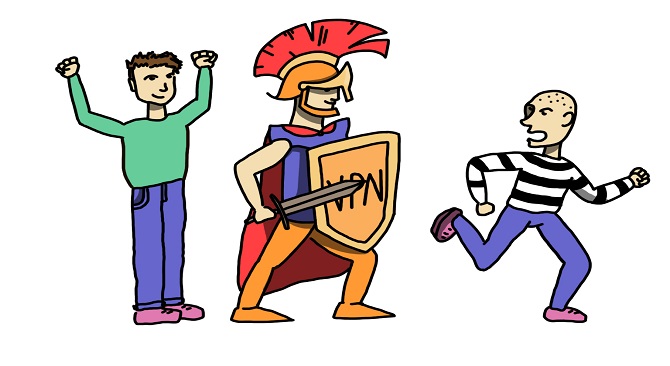
VPN is known as virtual private network which is an inscribed connection over the Internet from a gadget to a network. The encoded connection assistance ensures that insightful data is guardedly transmitted. It averts unlicensed populace from encroaching on the traffic and grants the user to deport work inaccessibly. VPN technology is utterly used in corporate domains.
Traffic on the virtual network is sent cautiously by building connections over the Internet known as a tunnel. VPN traffic from a gadget such as a computer or smartphone is encoded as it drives through this tunnel. Off premises employees can make use of virtual networks to have a reach of the corporate network.
VPN’S WORKING
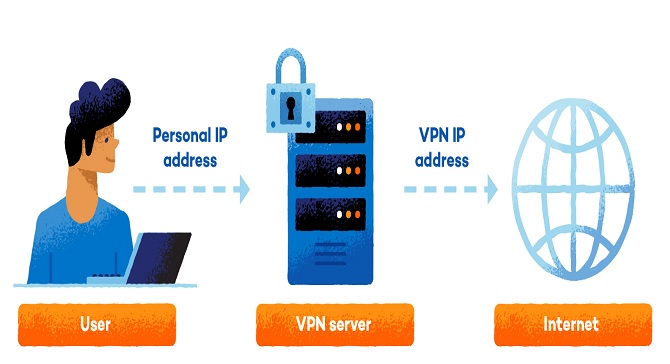
Connecting to a VPN is substantially very unpretentious. After signing up to a VPN source, it can be downloaded and installed as VPN software. Then a server is selected from which it needs to be connected to and the VPN will do the rest of the work.
When the link is put in order, the VPN system on a computer deciphers the data traffic and remits it to the VPN server through a shielded connection. The data also goes through the Internet Service Provider, but it can no longer eavesdrop because of the encryption.
A VPN conceals someone’s IP address by sanctioning the network, digressing it through a peculiarly built remote server managed by a VPN host. This articulates that if someone explores online with a VPN, the VPN server becomes the touchstone of the data. This derives that Internet Service Provider (ISP) and other third parties are unable to catch sight of which websites the person visits or what data that person sends and receives online. A VPN works like a dowel that turns all of the data into “blather”. Even if someone were to repossess another person’s data, it would be pointless.
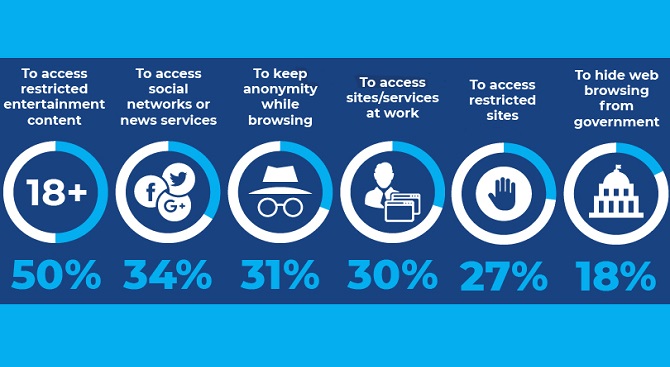
USAGE OF VPN’S
VPN is used to safeguard IP addresses and confidentiality. VPNs necessarily generate a data subway between a person’s local network and a departure vertex in another locality, which could be hundreds of thousands of miles away, making it appear as if the person is in another place. This kind of assistance empowers online liberty, or the propensity to access preferred apps and websites while being harped on.
There’s another faction to privacy. Without a VPN, a person’s internet service provider will be able to know the total browsing history. With a VPN, a search history can be hidden. That’s owing to the fact that a personage’s web task will be fettered with the VPN server’s IP address, not to his personal IP address. A VPN service granter might be having servers all over the map. That denotes a person’s search task could appear to emerge at any one of them. Take into consideration, search engines also record a person’s search history, but they’ll relate that information with an IP address that’s not of the person. Afresh VPN will keep an online activity private.
Benefits of VPN
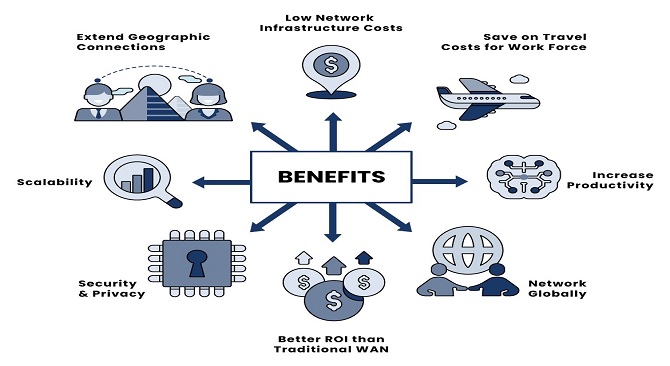
Prevent Data Restraining: Data restraining takes place when we have absorbed a peculiar proportion of accessible data, and the internet service provider (ISP) then choses to loitering the service down. If we have a VPN, we can circumvent a data limit, explicitly because not even our ISP can see how much data we are using. This may be largely supportive for employees who have to use data plans on their smart devices while acquiring the internet when on the road.
Network Flexibility: While a private network can assist a business to set in motion, the cost of lengthening the network can be proscriptive. If we use a VPN, we can provide an approach to many employees and remote workers concomitantly. We can also sprint key applications in cloud environs and give them access through the safe subway of the VPN.
This can incorporate whatever from email to fully-fledged applications that we would ordinarily run on a desktop computer. When employees link to the VPN, they obtain access to another computer that we use to run the application we require. Every employee with a login can access the VPN and therefore the application. Adding more employees is only a phenomenon of contributing more bandwidth, if essential, and the login testimonials to each team member.
Reduce Support Costs
With a VPN structure that assimilates cloud computing architecture, we have the fortuity to extricate a reasonable amount of money on aid services. As an illustration, with an on-site structure, the performance and maintenance of the intramural server is usually the job of the inner IT workforce. This may include hours of checking how well the server is working, whether all employees are attaining satisfactory productive capacity, and whether it is under threat by geeks or malware.
Furthermore, when a matter is distinguished, more time needs to be assigned to super scribing it and the by-product it may have given rise to within our organization.
With a VPN, although, all servicing, fulfilment checks, and security manoeuvres fall under the ambit of the service contributor. Their IT outlay is held up by a huge number of remunerating clients, making their cost per client fairly truncated. These cost economizing’s get passed on to us in the form of charge which is lower than what we would recompense to have a committed team manage their infrastructure.
To corroborate this is the case, it is sagacious to alertly examine the services the contributor puts forward to, as well as the kinds of hardware they are operating. More latter day integrands and security gauges frequently reverberate in a superior escapade for us, the client.
What does VPN stand for?
VPN hair stands for a virtual private network whose purpose is to provide the client privacy and security as the client communicates over the internet. The Internet was primarily designed to send chunks of information and data so anyone can easily rely on it as soon as possible. The connection of networking all over the world and country individually was relatively brand new and the nodes gradually went down.
Different kinds of applications with the client can use it can email, Facebook, messaging, web extra are all developed on top of internet protocol Core. With the increase in time, the standards of many apps have developed but not all of them were fully secured. Many information, data, and applications one lacking in security and privacy protection.
Due to a lack of privacy and security, there are many internet users who are attempting crimes like stealing peoples banking information, and spy on them for a whole range of harmful reasons.
For VPN comes a picture which creates a private tunnel over all the open internet all over the world. All the information, idea, data which you send is encapsulated in a certain private communication channel and encrypted so. Virtual private networks are very powerful and vital tools which help you to protect your data and information but they come with certain kinds of limitations.
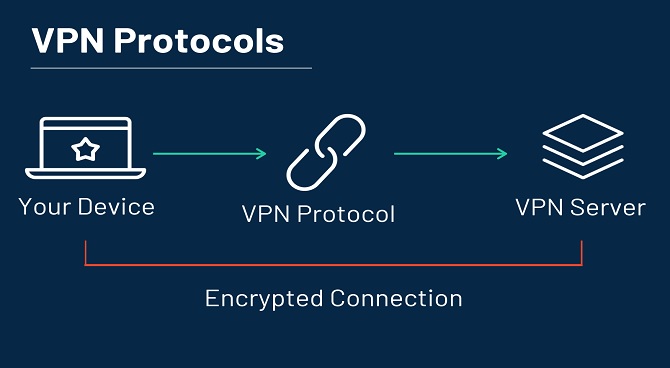
What are VPN protocols?
VPN Protocols are a bunch of rules and regulations which help you to create a connection between your personal device and the VPN proxy servers. Each and all VPN protocols are a combination of encryption methods and transmissions of protocols.
Open VPN
This VPN is the most powerful VPN as it is known for its security and speed. As it is an open-source protocol so it is available for anyone to verify That any developers are not doing any suspicious activities themselves.
IKEv2
It stands for internet key exchange version 2, which is a very efficient protocol and combined with IPsec protocol for efficient security. This protocol is mainly popular for mobile devices because it is easy to switch between mobile data and Wi-Fi networks.
PPTP
It stands for point-to-point tunnelling protocol which is an obsolete and very secure protocol and popular with free VPN services.
Why is it important to hide your IP address?
There can be many reasons which may be very crucial that why you need to hide your IP address but the biggest reason that you should hide your IP address is that the client can download any illegal material without being identified or tracked.
Another reason can be any kind of geographical restrictions and any kind of censorship. There is a certain kind of content that is restricted and blocked by the government in certain regions like China and the Middle East. Many private companies also use geo lock to their content to make it available in certain countries like it happens with YouTube why some countries like Germany E Block copyrighted content.
Other reasons can be e simply for more privacy and to prevent misuse of personal data and information. When the client accesses any kind of website or any kind of application the server connected with your IP address and attaches it to all the other kind of data the site can learn about you like it can be your browsing habits, your clicks and how long you spend your time on a particular or specific kind of page.
There are many arousing questions on VPNs, about its safety and usability. Check the given below FAQs about VPN, for greater insights.
What does a VPN do?
There are many kinds of work which are followed by VPN:
VPN conveniently provides security to the public Wi-Fi. For example, when the client is answering emails at a local cyber cafe or any kind of a coffee shop or scrolling to their social media at the workplace or airport or Mall except, there is a suspicious personality who is tracking your online activities. While using VPN the client can protect their data and information while they are on any other network.
It also provides privacy of the data from your internet service provider. Client’s internet service providers like Comcast, spectrum, or any other company whom the buyer is paying for the Wi-Fi every month has vital Access to your Internet data which can be dangerous if handed over to the wrong hands. In this case also VPN can help to secure your IP address from your own internet service provider.
Also, it secures the data from the apps and services which clients use on a daily basis. Therefore, we use many apps and websites every day like Facebook, Instagram, WhatsApp except for a vital amount of data of their uses. VPN will protect your apps and websites from getting it misused.
Here are some of the recent FAQs about VPN-
Q. What should I know before using a VPN?
Ans: There are a number of things one should know before using a Free VPN. For example the success and failure rate of the VPN, can that VPN affect your malware, VPNs do slow down your system, etc.
Q. Does a VPN protect passwords?
Ans: Your data like passwords are protected while you use VPN, but you need to be highly cautious about malfunctions or failures, this can help the hackers to acquire your passwords.
Q. Are VPNs legal?
Ans: It depends on countries if they make VPN legal or not. But, if we only talk about the USA, then Yes, VPN is totally legal in the USA.
Q. Are VPNs safe?
Ans: VPNs are considered to be one of the safest ways of preventing your browsers from hackers or any other unauthorized invasions. But it is a part of technology, so it is very important to use VPN judiciously.
Q. Is VPN safe for online banking?
Ans: Yes, VPNs are again considered as safe options to protect your information and data while you use net banking.